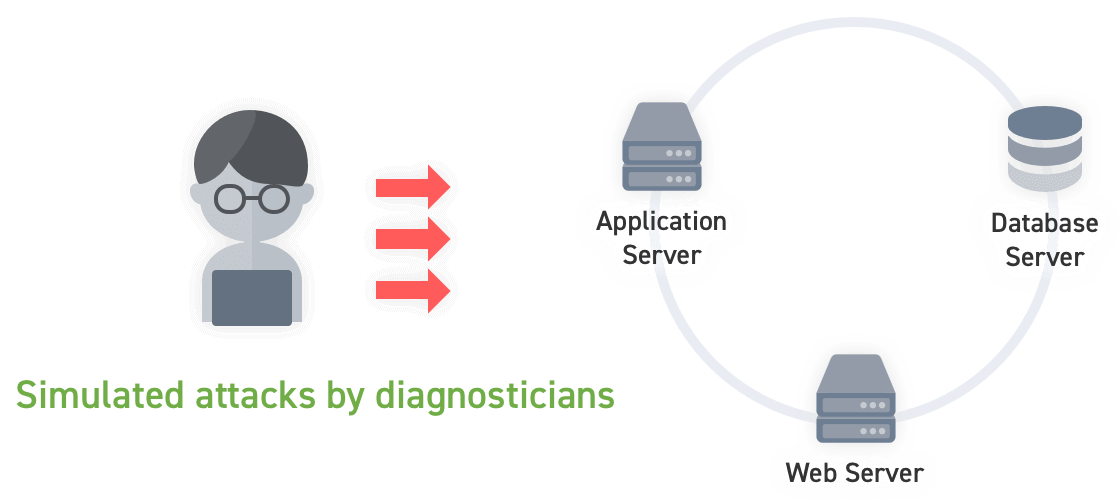
Web Application Vulnerability AssessmentFind vulnerabilities by launching pseudo-attacks.
The analyst takes the point of view of an attacker and launches a pseudo-attack on the target service to discover hidden vulnerabilities.
We provide our customers with highly accurate results by using both manual and automated diagnosis by our experienced diagnosticians. After the diagnosis, a detailed report on the discovered vulnerabilities will be prepared, and the reproduction procedure and countermeasures against the vulnerabilities will be reported in detail.