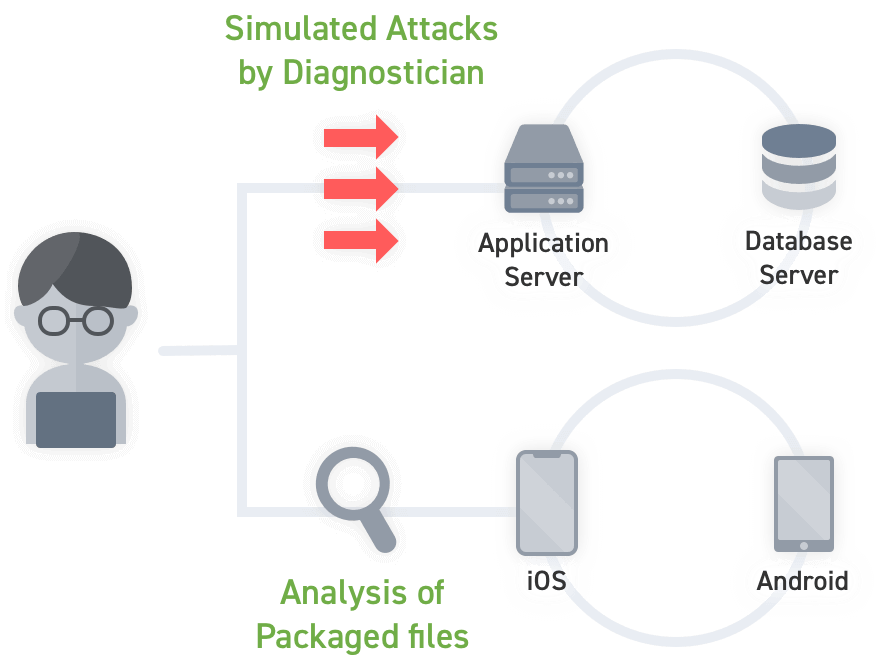
Smartphone Application Vulnerability AssessmentAnalysis of package files and vulnerability assessment for APIs
Analyze package files and perform vulnerability assessment for APIs used by the application.
We provide highly accurate results by using a combination of manual assessment by experienced assessors and supplementary assessment with tools. After the diagnosis is complete, a detailed report on the discovered vulnerabilities is prepared, and the reproduction procedure and countermeasures against the vulnerabilities are reported in detail.